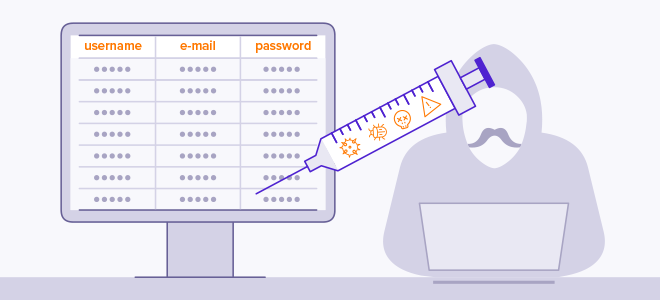
SQL INJECTION
One of the injection attack techniques SQL injection The basis of the vulnerability is the use of data received from the user in SQL queries.
What is SQL Injection?
We can define SQL Injection as obtaining the desired information from the database of the system after the SQL codes are injected into the target system.
A developed web application can be linked to a database. An application that searches the phone book is a simple example. What you need to do as an end user is to enter a phone number in the box presented to you and press the call button. The phone number you have written will be included in the relevant SQL query and the results obtained by searching will be printed on the screen. The possible SQL query that will occur is given below.
- select * from directory where number='{SIZDEN_COMING_PHONE_NUMBER}'
Now suppose there is a member search box. The SQL query formed after the word typed in this search box is as follows. Return all (*) records that match the name column with “Eymen DEMİR”.
mysql > select * from members where surname='Eymen Demir'

We can simply manipulate this member search query. With a logical equality expression, we can ensure that all records arrive. We must write an expression such that it is true in all cases.
Payload: '1' or '1'='1'
mysql > select * from members where firstname='1' or '1'='1'
with the specified payload SQL Injection The resulting expression is as follows:
1 the one which... or (or) 1=1 bring it. Name and surname 1 there is no one in the database. However or always after the conditional 1=1 true(true) It will be ensured that all records are displayed on the screen.

By simply manipulating the SQL query with the expected value, we ensured that all records were fetched.
What are the SQL Injection Types?
- Boolean-based Blind SQL Injection: It is the SQL Injection technique that must be applied blindly, where no error message is printed on the screen.
- Error-based SQL Injection: As the name suggests, it is a type of SQL injection based on error messages. “,'#”< It emerges with the use of characters such as
- UNION Query SQL Injection: It is an injection type in which several different selections are made together by using the "union" keyword of the number of columns during the injection.
- Time-based blind SQL Injection: It is a blind injection type that does not give an error message. on target SQL Injection The "sleep" function is used to detect a vulnerability.
SQL Injection In order to be protected from attacks, the inputs received from the users in the systems should be carefully controlled and filtered.