Os Command Injection (Operating System Command Injection)
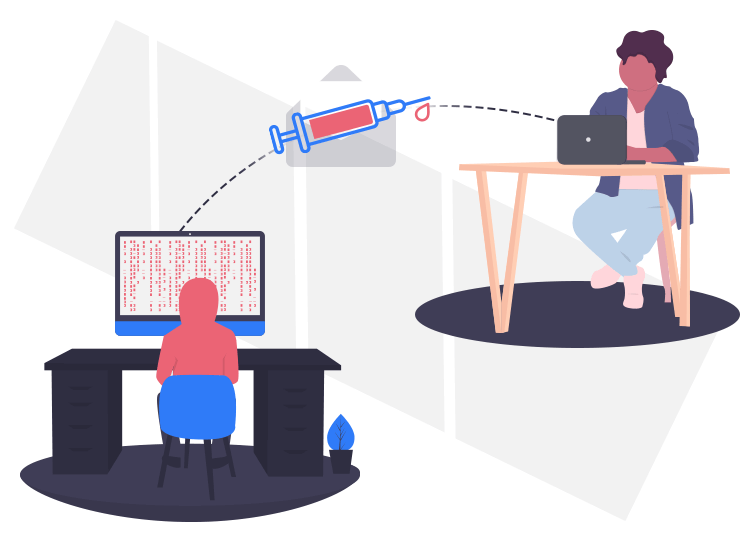
in english OS Command Injection Although it is not used much in our language, Operating System Command Injection This vulnerability is called OWASPIt is in the Injection category, which ranks first in the most popular vulnerabilities published by . Before talking about the details, it is necessary to mention what this weakness is.
What is Os Command Injection?
Exactly, Operating System Command Injection, is a web application vulnerability. It allows operating system (OS) commands to be executed on the server running this web application. In other words, this process is like running commands on CMD on Windows and terminal on Linux. The things an attacker can do with someone at the machine are almost the same.
How Does Os Command Injection Affect the System?
This vulnerability gives the attackers the authority to run commands without permission on the system. Depending on the installation of the application and the configuration of the process executing it, it may cause the process to increase its privilege level or create a remote reverse shell that allows full interaction of the attacker. In fact, the attacker can do just about anything the system allows. Therefore, it is a very dangerous and serious vulnerability.
How Can Os Command Injection System Be Detected?
OS Command Injection penetration tests It is one of the first vulnerabilities to be checked. If you are asking what is Penetration Testing, you can take a look at this article and get service from the address below.
So, how can we detect this vulnerability? Client input is used for the application to execute a command. The status is evaluated according to the output so that the Os Command Injection vulnerability can be detected.
How to Avoid Os Command Injection?
There are some techniques that can be applied to prevent the exploitation of this vulnerability;
- Checking the input format. (Example: numeric expressions, word count, etc.)
- Creating a white-list for the control of the entries, that is, only the allowed words can be used.
- Using the Die function after using the Header function so that subsequent entries are invalid
- The input consists of only alphanumeric characters, that is, only numbers and letters are used.
Moreover cyber security consulting take regularly penetration test (pentest) to make you free from these attacks, from cyber criminals will protect. Remember, early detection saves lives.