Microsoft MSHTML Remote Code Execution Vulnerability CVE-2021-40444
General Attack Summary
The origin of the CVE-2021-40444 vulnerability is the ActiveX feature in Internet Explorer software. Although few people use Internet Explorer these days, this outdated browser remains a component of modern Windows operating systems, especially Microsoft Office applications such as Word and PowerPoint for rendering Web content. The old Internet Explorer engine is used for .
To exploit the CVE-2021-40444 vulnerability, attackers direct the target device to a web address via a Microsoft Word document. via this website ministry.cab malware with extension is downloaded using ActiveX, ministry.cab located in championship.inf It actually contains the Cobalt Strike malware.
After the target person clicks on this Word document containing malware, the device is taken over by the attacker. This process is contrary to the normal flow of the Word application and ActiveX is abused for the downloading process. Control.exe, seen through the Process Tree, was detected using the vulnerability coded CVE-2021-40444.AppData/Local/Temp/Low” The malware downloaded to the folder is executed.

JavaScript Content Specially Prepared for Exploitation of CVE-2021-40444 Vulnerability
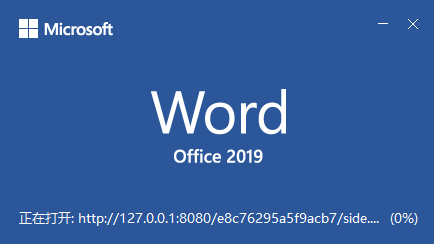
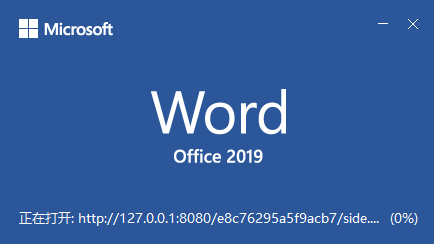
As soon as the Word file is opened on the target device, it sends a query via ActiveX to an address named side.html to exploit the vulnerability.
The Web address used to exploit the vulnerability can be seen in String format in the Word document (“document.xml.rels”). The section marked in red is the web address of the attacker used during the exploit process. at the beginning of the web address that contains Malware. mhtml: The tag indicates that MSHTML is used, which is a feature of Microsoft Office products.

JavaScript Code Decoded from Side.html
side.html content contains obfuscated JavaScript code. As a result of the analysis, this code was opened and made meaningful.
In the code fragment seen in the picture, the .cab file (Malware) downloaded from a certain server is downloaded to the "/AppData/Local/Temp/Low" location determined by the attacker with the help of ActiveXObject, and then, as the 2nd stage, rundll32 in .cpl format via Control.exe. located in .cab file with exe The championship.inf malware is run.

Used as malware by the attacker ministry.cab "" in the Cabinet file with the extension "championship.inf” can be run with rundll32.exe (DOS MZ executable).

Microsoft MSHTML Remote Code Execution Vulnerability Attack Flow
Attackers can create an ActiveX control in a Microsoft Office document using the MSHTML rendering engine. After the attacker prepares an ActiveX control containing malicious code embedded in an MS Office document, he must deliver this document to the user. It mostly uses the Phishing (MITRE ATT&CK T1566) technique to send documents containing Malware as email attachments or links. After that, the user must open the document containing the malware to trigger the vulnerability.
After the document containing the Malware is opened, the Exploit is triggered and the malware downloaded from the attacker web address is seen in the picture.

Reducing the Attack Surface and Precautions That Can Be Taken Against Security Vulnerabilities
- Turn off ActiveX controls
Save the Registry code below as .reg and run it with Admin rights, then restart the device.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\0]
“1001”=dword:00000003
“1004”=dword:00000003
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\1]
“1001”=dword:00000003
“1004”=dword:00000003
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2]
“1001”=dword:00000003
“1004”=dword:00000003
[HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3]
“1001”=dword:00000003
“1004”=dword:00000003
- Set Microsoft Office software to automatically open documents received from the Internet in Protected View and block macros.
A patch has not yet been released by Microsoft for this security vulnerability.
CVE-2021-40444 Indicators of Compromise (IOCs) Data
.DOCX file #1 (A Letter before court 4.docx):
MD5 1d2094ce85d66878ee079185e2761beb
SHA-1 53b31e513d8e23e30b7f133d4504ca7429f0e1fe
SHA-256 938545f7bbe40738908a95da8cdeabb2a11ce2ca36b0f6a74deda9378d380a52
.DOCX file #2 (PRD.docx):
MD5 d1837399df37757e5ebd04f45746301a
SHA-1 f43ebedb86db817b208aebdf88e08163f239b832
SHA-256 199b9e9a7533431731fbb08ff19d437de1de6533f3ebbffc1e13eeffaa4fd455
.DOCX file #3 (Project details (1).docx):
MD5 265be11d746a90d8b6a6f9eda1d31fb7
SHA-1 1a528a5964cd18d8ce7a47e69e30ef1163407233
SHA-256 5b85dbe49b8bc1e65e01414a0508329dc41dc13c92c08a4f14c71e3044b06185
.DOCX file #4 (App description.docx):
MD5 6f194654557e1b52fb0d573a5403e4b1
SHA-1 d05fc61894cb7652dce69edd6e4cf7e4e639754a
SHA-256 3bddb2e1a85a9e06b9f9021ad301fdcde33e197225ae1676b8c6d0b416193ecf
.DOCX file #5 (court.docx):
MD5 55998cb43459159a5ed4511f00ff3fc8
SHA-1 9bec2182cc5b41fe8783bb7ab6e577bac5c19f04
SHA-256 d0e1f97dbe2d0af9342e64d460527b088d85f96d38b1d1d4aa610c0987dca745
.HTML file (side.html):
MD5 4c80dc9fb7483214b1613957aae57e2a
SHA-1 e5f2089d95fd713ca3d4787fe53c0ec036135e92
SHA-256 d0fd7acc38b3105facd6995344242f28e45f5384c0fdf2ec93ea24bfbc1dc9e6
.CAB file (ministry.cab):
MD5 e770385f9a743ad4098f510166699305
SHA-1 56a8d4f7009caf32c9e28f3df945a7826315254c
SHA-256 1fb13a158aff3d258b8f62fe211fabeed03f0763b2acadbccad9e8e39969ea00
.DLL file (payload.dll):
MD5 0b7da6388091ff9d696a18c95d41b587
SHA-1 6c10d7d88606ac1afd30b4e61bf232329a276cdc
SHA-256 6eedf45cb91f6762de4e35e36bcb03e5ad60ce9ac5a08caeb7eda035cd74762b
.XML file (document.xml.rels):
MD5 5890b8eed650223f37bb358c095306f3
SHA-1 7eab2182e3f851ab4cd026ba5f26a59040c0c8bc
SHA-256 049ed15ef970bd12ce662cffa59f7d0e0b360d47fac556ac3d36f2788a2bc5a4